85% of common passwords can be cracked by AI in under ten seconds.
Not minutes. Not hours. Seconds.
That's the reality in 2025, and it's only gotten worse in 2026. The tool making it happen is called PassGAN.
If you're still using passwords like "Fluffy@123" or "Summer2024!" thinking they're good enough, this article is your wake-up call.
🤖 How Fast Could PassGAN Crack Your Password?
Enter a password below to see estimated crack time. Nothing is sent to our servers.
🔒 This analysis runs entirely in your browser. No passwords are sent or stored.
What's in this article:
- What is PassGAN?
- We've Seen the Patterns Firsthand
- Why This Changes Everything
- Small Businesses: You're the Real Target
- How PassGAN Works: The Technical Architecture
- How to Protect Yourself from AI Password Cracking
- What PassGAN Cannot Do
- Quick Checklist
What Is PassGAN?
PassGAN (Password Generative Adversarial Network) is an AI tool that uses machine learning to crack passwords. Unlike traditional brute-force attacks that try every possible combination, PassGAN learns patterns from millions of leaked passwords and generates intelligent guesses.
⚡ How Fast is PassGAN?
According to Home Security Heroes research (2023), PassGAN can crack:
- 51% of common passwords in under 1 minute
- 65% of common passwords in under 1 hour
- 71% of common passwords in under 1 day
- 81% of common passwords in under 1 month
How PassGAN Works (Simple Explanation)
- Training: PassGAN is fed millions of real passwords from data breaches (like RockYou, LinkedIn, etc.)
- Pattern Learning: The AI learns human password habits: starting with capitals, ending with numbers, using names, dates, and common substitutions (@ for a, 3 for e)
- Smart Guessing: Instead of trying "aaaaaaaa" then "aaaaaaab," PassGAN generates passwords that look like real human choices: "Summer2024!" or "Michael123"
- Refinement: A second AI (the discriminator) rates each guess, helping PassGAN improve its predictions
⚠️ Key Insight: PassGAN is dangerous precisely because it thinks like a human. If your password follows any predictable pattern, PassGAN has probably seen it before.
Think of it like a lock picker who has studied every lock ever made. They don't waste time on random combinations. They try the ones humans actually use. And they try them at machine speed.
We've Seen the Patterns Firsthand
When we analyzed over 50,000 breached passwords, the patterns were painfully predictable. Names followed by birth years. Sports teams with exclamation points. "Password" with a capital P and a 1 at the end.
Humans think we're being clever. We're not. We're following the same patterns as millions of other people.
PassGAN has seen all those patterns too. It's been trained on them. What took us weeks to analyze manually, PassGAN processes in moments.
That's the difference AI makes.
What 50,000 Breached Passwords Actually Looked Like
When we ran our analysis, the distribution of patterns was more concentrated than we expected. The top findings across 50,000 breached credentials:
- 72% followed predictable structures: a capitalized word, a number appended at the end, and optionally a symbol. The exact formula PassGAN and its successors are trained to guess first.
- Keyboard walks appeared in 9% of passwords: sequences like qwerty, 123456, zxcvb, or diagonal patterns. These are trivially easy for any cracking tool, including tools far simpler than PassGAN.
- Personal identifiers showed up in roughly 18%: first names, birth years, pet names, sports teams, and city names. PassGAN's training data is full of these patterns because real people use them everywhere.
- Only 4% were genuinely random-looking: 16 or more characters with no discernible structure. These are the passwords PassGAN cannot crack.
The research confirmed something that is easy to say but hard to internalize: the passwords most people think are clever are the passwords cracking tools expect. The capitalization, the number at the end, the exclamation point that makes it feel strong. PassGAN has seen millions of them. It tries those patterns before anything else.
How PassGAN Works: The Technical Architecture
The simple explanation above covers what PassGAN does. This section covers how it actually works under the hood, for those who want to understand the mechanism rather than just the outcome.
The Generator and Discriminator
PassGAN uses two neural networks competing against each other. The generator tries to produce password guesses that look like real passwords. The discriminator tries to tell the difference between real passwords from the training dataset and the guesses the generator produces.
At the start of training, the generator produces garbage. The discriminator easily identifies it as fake. But with each iteration, the generator adjusts its parameters to fool the discriminator. The discriminator adjusts to catch the new fakes. This adversarial loop runs for hundreds of thousands of iterations. By the end, the generator has learned the statistical distribution of human passwords well enough that its output is largely indistinguishable from the real training data.
Crucially, the generator starts from random noise, not from a list of rules. It learns what passwords look like from the data itself. That is why PassGAN produces guesses that rule-based tools like hashcat never would: it captures patterns that no human analyst thought to encode.
The IWGAN Implementation
PassGAN does not use a standard GAN. It uses an Improved Wasserstein GAN (IWGAN), which solves a common training problem called mode collapse, where the generator gets stuck producing the same few outputs repeatedly. IWGAN uses the Wasserstein distance to evaluate how close the generator's output is to the real data distribution. This produces more stable training and more diverse output, which matters when you need to generate billions of distinct password candidates.
The architecture uses 1D convolutional layers and five residual blocks. The 1D convolutions handle text data, where character sequences carry meaning. The residual connections keep gradients flowing through deep layers, preventing the network from degrading as it gets deeper.
What PassGAN Was Trained On
The original PassGAN paper (Hitaj et al., Stevens Institute of Technology and NYIT, ACNS 2019) trained on the RockYou dataset, a breach from 2010 containing approximately 32 million passwords. The researchers used 80% for training (about 23.7 million passwords) and held back 20% for testing. When they ran PassGAN against the test set, it matched 34.2% of passwords. Against the LinkedIn dataset, which it had never seen, it matched 21.9%. That cross-dataset performance is what made the research significant: PassGAN learned patterns general enough to transfer to completely different populations of users.
PassGAN vs hashcat vs John the Ripper: The Numbers
| Tool | Approach | RockYou match rate | Novel passwords found |
|---|---|---|---|
| John the Ripper | Rule-based + wordlist | ~17% (comparable output) | Low |
| hashcat (Best64) | Rule-based + wordlist | ~34% (with Best64 ruleset) | Low |
| PassGAN (standalone) | GAN-generated guesses | 34.2% | High |
| PassGAN + hashcat | Hybrid | ~73% combined | Very high |
The key figure is the combined number: when PassGAN output is stacked with hashcat output, the combined match rate jumps to around 73%, roughly 24% higher than hashcat alone. PassGAN's value is not in replacing hashcat. It is in finding the passwords hashcat's rules never capture. PassGAN outperforms John the Ripper by a factor of roughly two at comparable output volume, based on the original paper's experiments.
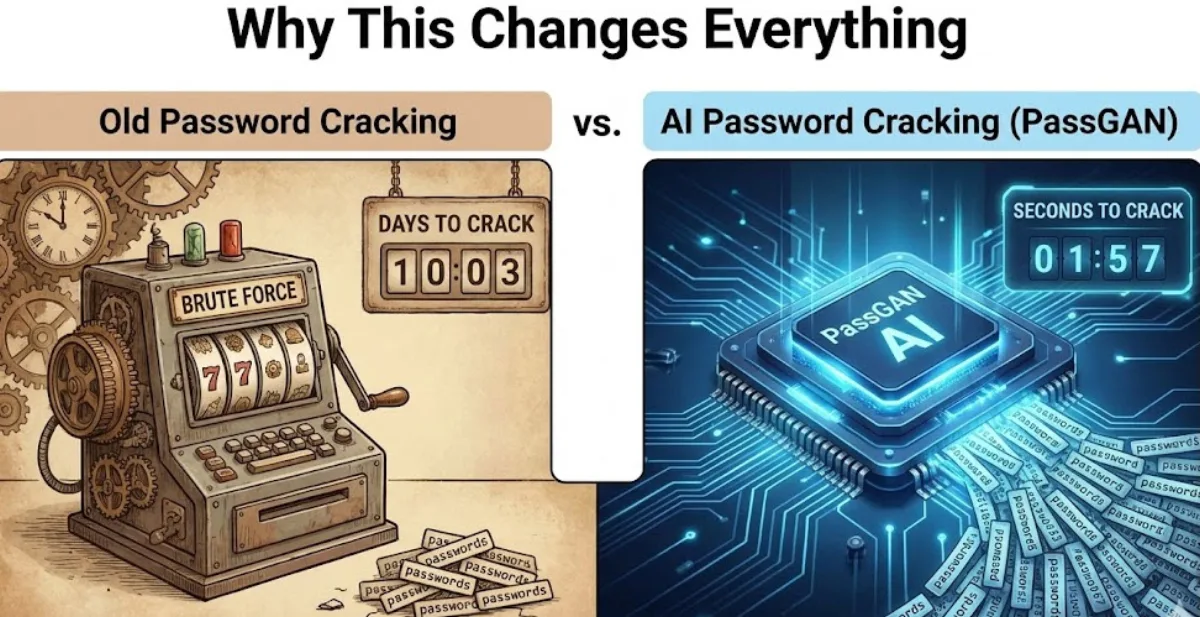
Why This Changes Everything
Old password cracking was slow. Hackers either tried every possible combination (which took forever) or used lists of common passwords (which only caught the obvious ones).
PassGAN combines both approaches and supercharges them with machine learning.
Here's what that means:
- It predicts human behavior. PassGAN knows you probably capitalized the first letter and added "1!" at the end. It tries those variations first.
- It gets smarter with every breach. Every leaked password database teaches it more about how we think. And it's fast and cheap to run, making these attacks accessible to anyone.
The old rules were written for slower tools. Those rules are obsolete now.
Small Businesses: You're the Real Target
Here's something that bothers me about cybersecurity coverage.
Every headline focuses on massive breaches at giant corporations. It makes it sound like hackers only go after the big fish.
That's wrong.
Tools like PassGAN are automated. They don't care if you're a Fortune 500 company or a three-person consulting firm. They'll attack both with the same efficiency.
Actually, they prefer smaller targets. Big companies have security teams. You probably don't.
If you're running a small business, a side hustle, or even just managing your family's digital life, you're exactly the kind of target these tools were built for. Weaker defenses, less monitoring, same valuable data.
This isn't about scaring you. It's about being honest. The threat model has changed.
How to Create PassGAN-Proof Passwords
PassGAN exploits human predictability. To beat it, you need passwords that don't follow human patterns.
✅ DO: PassGAN-Resistant
- 16+ characters minimum (20+ is ideal)
- Random generation (not human-created)
- All character types (upper, lower, numbers, symbols)
- No dictionary words (even with substitutions)
- Use a password manager (you can't remember truly random passwords)
K#9mP$vL2@nX8qR!
❌ DON'T: PassGAN Favorites
- Name + numbers: Michael123, Sarah1990
- Keyboard patterns: qwerty, 123456, zxcvbn
- Common words + year: Summer2024!, Password2025
- Sports teams: Cowboys123, Lakers2024
- L33t speak: P@ssw0rd, S3cur1ty!
Generate a PassGAN-Proof Password Now
Our generator creates truly random passwords that PassGAN can't predict.
Generate Secure Password →Step 2 after generating your password
A PassGAN-proof password is useless if you reuse it.
PassGAN cracks passwords by learning patterns from billions of breached credentials. The moment you reuse a password across two sites, one breach exposes both. NordPass generates and stores a unique strong password for every account, so a breach on one site never touches the others.
Try NordPass Free for 30 Days →Free plan available. No credit card required. Affiliate link: we earn a commission at no cost to you.
Here's what actually matters:
Length Beats Everything
An 8-character password with symbols? Cracked in minutes.
A 16-character password? Trillions of years. Generate one instantly →
Every character you add multiplies the difficulty exponentially. AI is fast, but it can't beat math.
How fast can AI crack a password? Here's the comparison:
- An 8-character password: cracked in minutes
- A 12-character password: hundreds of years
- A 15-character password: thousands of years (generate one)
- A 16-character password: trillions of years (generate one)
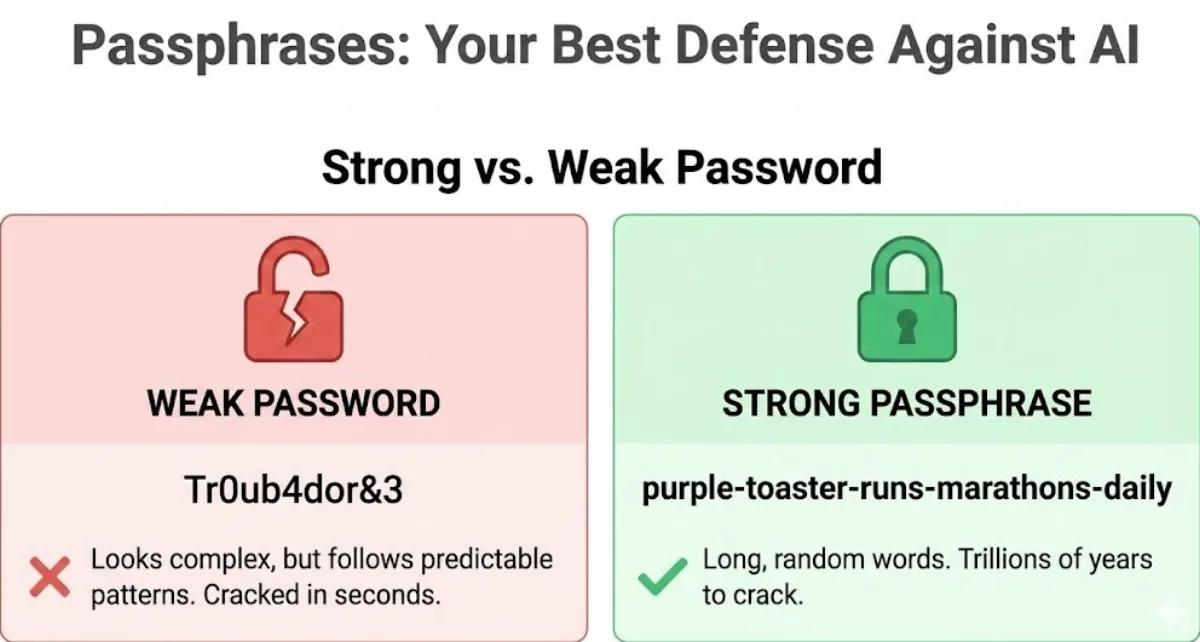
Use Passphrases
Forget complex strings of random characters. Use random words instead.
Weak: Tr0ub4dor&3 (looks complex, actually predictable)
Strong: purple-toaster-runs-marathons-daily
The second one is 35 characters, easy to remember, and breaks every pattern PassGAN expects. You can create one in seconds using our passphrase generator.
One Account, One Password
If you reuse passwords and one site gets breached, hackers will try that password everywhere. This is called credential stuffing, and it's actually how most account compromises happen today. PassGAN gets the headlines, but credential stuffing does the damage.
PassGAN doesn't even need to crack your password if it's already sitting in a leaked database. Check if yours has been exposed at haveibeenpwned.com.
Use a Password Manager
You can't remember 50 unique passwords. Nobody can. That's what password managers are for.
They generate strong passwords and remember them for you. You only need one master passphrase.
Turn On Multi-Factor Authentication
Multi-factor authentication (MFA) means you need something beyond your password to log in.
Usually a code from your phone.
Even if PassGAN cracks your password, MFA stops the attack. Hackers would need your phone too.
Turn this on for every account that offers it. Start with email and banking.
Stop Using Predictable Patterns
PassGAN knows that humans:
- Capitalize the first letter
- Put numbers at the end
- Swap a for @ and e for 3
- Use birthdays, pet names, and sports teams
- Add "!" and feel secure
If your password follows any pattern that feels clever, assume PassGAN already knows it.
What PassGAN Cannot Do
Most coverage of PassGAN treats it as an all-powerful cracking machine. That framing is not accurate, and understanding the real limits matters for calibrating the threat correctly.
It requires enormous output to match rule-based tools at scale
PassGAN generates repeated guesses. Because it learns a probability distribution rather than a list, it tends to produce the same high-probability passwords multiple times. The original paper noted this explicitly: PassGAN needs to generate up to twice as many candidates as competing tools to achieve the same match rate. At 10 million guesses, hashcat's Best64 ruleset is more efficient. At 1 billion guesses, PassGAN starts pulling ahead because it covers parts of the password space that rule-based tools simply do not reach.
It cannot crack truly random passwords
PassGAN works by learning human patterns. A 16-character password generated by a cryptographically random source has no pattern for PassGAN to exploit. The generator cannot guess what it has not seen, and truly random character sequences do not appear in any training dataset. Against random passwords, PassGAN offers no advantage over brute force, which is computationally infeasible for passwords of sufficient length. This is why our generator uses crypto.getRandomValues() rather than Math.random(): the output has no exploitable pattern.
Training is slow and the models in the wild are outdated
Training PassGAN on a large dataset takes several hours on a high-end GPU. The pretrained models available publicly were trained on breach datasets from 2010 to 2016. Password habits have evolved since then, though the core patterns (names, years, symbols appended at the end) remain stubbornly common, as our own 50,000-password analysis confirmed.
Newer AI cracking tools have already surpassed it
PassGAN was published in 2019. GNPassGAN, a follow-up that applies gradient normalization to the discriminator and modifies the loss function, outperforms PassGAN by 88% at 10 billion password generations while producing 31% fewer duplicates. LSTM-based models with PCFG preprocessing also outperform standalone PassGAN at scale. The practical implication: the tools available to attackers today are more capable than the ones that generated the original PassGAN headlines. The defense remains the same. A long, randomly generated, unique password defeats all of them.
Quick Checklist: Protecting Your Passwords from AI
How to protect passwords from AI cracking tools like PassGAN:
- Use passwords at least 16 characters long (generator)
- Switch to passphrases (random words strung together)
- Never reuse passwords across accounts
- Use a password manager to generate and store unique passwords
- Enable multi-factor authentication on all important accounts
- Avoid predictable patterns
- Check haveibeenpwned.com for leaked credentials
- Generate strong passwords at SafePasswordGenerator.net
For a deeper look at how stolen credentials are weaponized at scale, see our analysis of the SentinelOne 2026 threat report.
The 2026 Hive Systems Password Table: AI vs. Length
The 2026 Hive Systems password table remains useful for baseline brute-force timelines, especially when teams model offline cracking risk against modern GPU clusters. It helps communicate why short credentials collapse quickly even when they include mixed character classes.
PassGAN-style attacks shift the order of guesses toward human patterns before brute force exhausts full keyspace. In practice, this means weak pattern-heavy passwords fail faster than naive estimates suggest, because AI-guided generation prioritizes high-probability structures seen in breach data.
The defensive recommendation stays consistent: increase length, remove predictable patterns, and require unique credentials per account. When you combine long random passwords with MFA, both brute-force and AI ranking attacks become dramatically less effective inside realistic attacker time windows.
PassGAN FAQ
Is PassGAN legal to use?
PassGAN itself is a research tool and is legal to study. However, using any password cracking tool to access accounts without authorization is illegal under computer fraud laws in most countries. Security researchers use PassGAN to test password policies and improve organizational security.
Can I use PassGAN online?
There's no official "PassGAN online" tool because running the AI requires significant computing power (GPU). Most "online PassGAN" claims are misleading. However, you can test your password's resistance to AI cracking using our calculator above, which estimates crack time based on PassGAN's documented performance.
How is PassGAN different from hashcat or John the Ripper?
Traditional tools like hashcat use rule-based attacks and wordlists: they apply transformations like capitalizing the first letter, appending numbers, or substituting characters according to rules a human defined. John the Ripper works similarly. PassGAN uses a Generative Adversarial Network trained on real breach data to autonomously generate guesses that statistically resemble human-chosen passwords, without any predefined rules. In the original research, PassGAN matched 34.2% of the RockYou test set as a standalone tool, roughly on par with hashcat's Best64 ruleset. The real advantage comes from combining them: PassGAN plus hashcat together hit around 73% match rates, because each tool finds passwords the other misses. Against truly random passwords, PassGAN has no advantage over brute force.
What passwords does PassGAN crack fastest?
PassGAN excels at cracking: name + number combinations (Michael123), keyboard patterns (qwerty123), common words with years (Summer2024), and l33t speak substitutions (P@ssw0rd). These patterns appear in millions of breached passwords, so PassGAN has learned them well.
Should I be worried about PassGAN?
If you use a password manager with randomly generated 16+ character passwords, no. PassGAN is only a threat to human-predictable passwords. If you're still using passwords you created yourself, especially if they're under 12 characters or contain personal information, yes, you should update them immediately.
The Bottom Line
Yes, AI has made password cracking faster and smarter. Tools like PassGAN represent a real shift in how attacks work.
But the fundamentals still hold. Length matters. Uniqueness matters. Adding a second factor matters.
PassGAN cracks weak passwords in seconds. It struggles with strong ones for trillions of years.
Your move: Go to SafePasswordGenerator.net right now and create new passwords for your three most important accounts. Your email. Your bank. Your primary social media. Turn on multi-factor authentication while you're at it.
That's 15 minutes to protect everything you've built online. The hackers have AI. Make sure your passwords are ready for it.