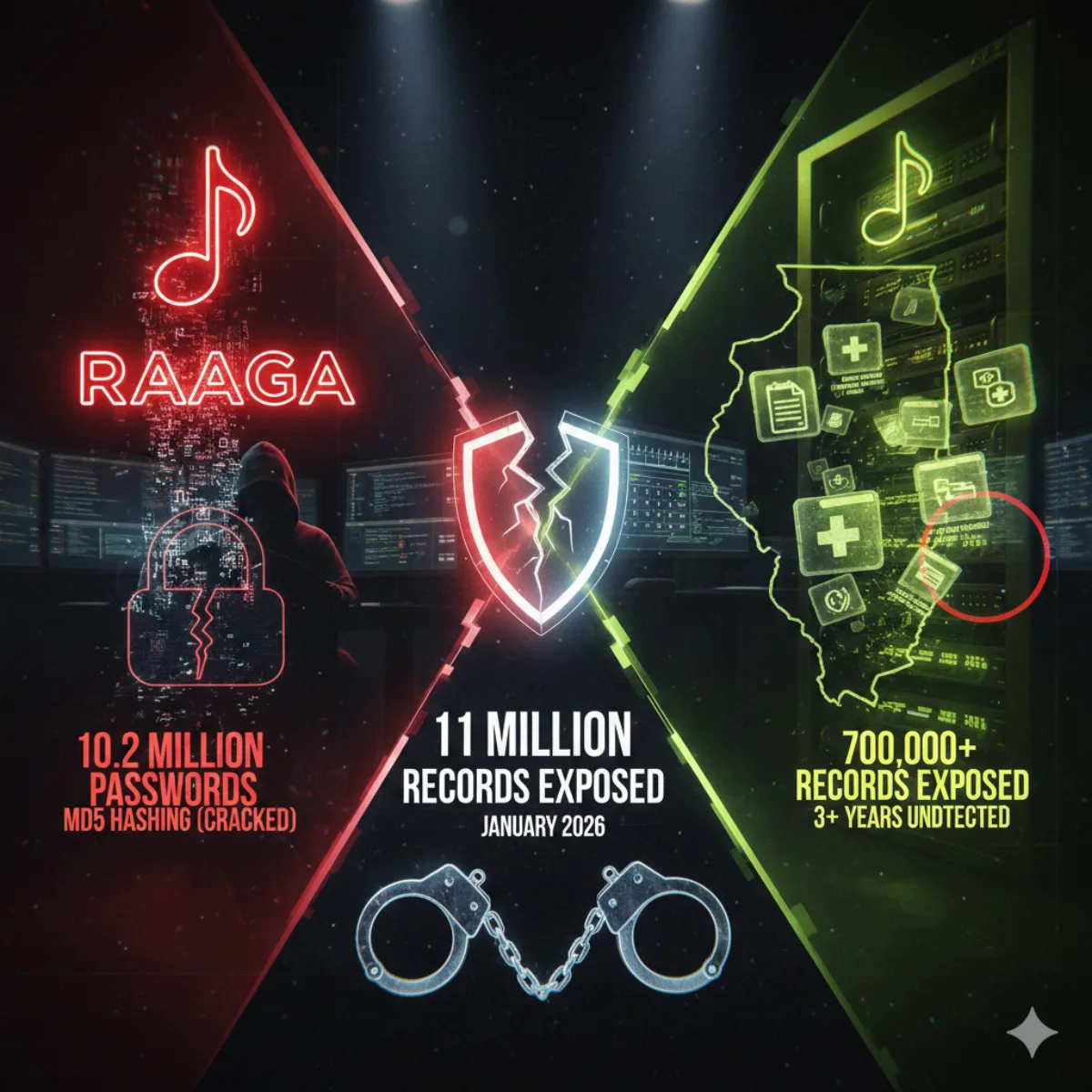
What Was Exposed in the Raaga and Illinois DHS Breaches?
Two major data breaches hit the news in January 2026. One exposed passwords stored with unsalted MD5 hashing, a method hackers cracked over 20 years ago. The other left government records sitting on the open internet for three years. Here is the critical breakdown:
- Raaga: Emails, names, birthdates, locations, and passwords stored using unsalted MD5 hashing
- Illinois DHS: Addresses, case numbers, medical plan details (672K); names, addresses, referral info (32K)
- Total records exposed: Over 11 million
- Exposure timeline: Illinois data was vulnerable for 3+ years before discovery
- Biggest risks: Credential stuffing attacks and long-term identity theft
Key takeaway: Raaga stored passwords using a method hackers cracked 20 years ago. Illinois left government records sitting on the open internet for 3 years. If you reused passwords anywhere, criminals are probably already testing them on your other accounts right now.
These breaches matter now because the stolen data is already being weaponized in credential stuffing attacks, not sitting in an archive. If you had an account on Raaga or interacted with Illinois DHS programs between 2021 and 2025, your information may already be in circulation.
After 10+ years working in DevSecOps across healthcare, fintech, and government systems, I can tell you these breaches reveal something worse than a security failure. They reveal negligence.
How the Raaga Data Breach Exposed 10.2 Million Passwords
Indian music streaming platform Raaga confirmed that attackers accessed user records in December 2025. The stolen data is reportedly circulating in breach-trading communities. The breach was added to Have I Been Pwned in January 2026.
What was leaked:
- 10.2 million unique email addresses
- Names, gender, age, and birthdates
- Geographic location data including postcodes
- Passwords stored as unsalted MD5 hashes
That last point is the problem. MD5 is a hashing algorithm that security professionals stopped recommending over a decade ago. Storing passwords with unsalted MD5 in 2026 is like locking your front door with a piece of wet string.
If you used the same password on Raaga that you use on other accounts, those accounts are now at risk. Attackers will use credential stuffing attacks to test your leaked password against banking sites, email providers, and social media platforms.
How the Illinois DHS Data Breach Went Undetected for 3+ Years
The Illinois Department of Human Services disclosed in January 2026 that a misconfigured system exposed records belonging to approximately 700,000 residents. The data was vulnerable from as early as April 2021 until September 2025.
Three years. No one noticed.
What was exposed:
| Group | Records | Data Types |
|---|---|---|
| Medicaid/Medicare Savings Program | 672,000+ | Addresses, case numbers, demographics, medical plan info (names NOT exposed) |
| Division of Rehabilitation Services | 32,000+ | Names, addresses, case details, referral information |
The DRS exposure is more severe because it includes names linked to disability services records. That combination makes targeted phishing and identity theft significantly easier.
Government agencies hold data you cannot change. Your Social Security number, your address history, your relationship with assistance programs. Once exposed, that information stays exposed.
Why Raaga's Password Storage Was So Bad (Explained Simply)
When you create a password on a website, that site is not supposed to store your actual password. Instead, they run it through a scrambler (called a "hash") that turns "MyDog2024" into something like "5d41402abc4b2a76b9719d911017c592". If hackers steal the database, they should only get the scrambled version, not your real password.
Here is the problem: Raaga used an old, broken scrambler called MD5.
Think of it like a lock on your front door:
- A modern password scrambler is like a high-security deadbolt. Even if someone gets a copy of your key shape, it takes years to figure out how to make a working key.
- MD5 is like a lock from 1991 that locksmiths figured out how to pick in 2004. Security experts have been saying "stop using this lock" for over 20 years.
- "Unsalted" MD5 is even worse. It means Raaga used the same broken lock for everyone, so hackers can use a master cheat sheet to open millions of locks at once.
How bad is it?
Hackers have already built giant lookup tables with billions of pre-cracked passwords. If your Raaga password was "Summer2024" or "Password123" or anything remotely common, it is already in those tables. The hackers do not need to guess. They just look it up.
On modern GPUs, unsalted MD5 hashes can be tested at billions per second. Many 10-character passwords, especially common patterns like "Summer2024" or "MyDog2020", can fall in seconds.
Better scrambling methods exist and have existed for years. They take minutes to set up. The only reason Raaga was still using MD5 in 2026 is that nobody in charge cared enough to fix it.
How Attackers Use Breached Passwords (Step-by-Step)
Understanding the attack chain helps you see why unique passwords matter:
- Breach data appears on forums: Stolen databases get sold or shared on dark web marketplaces
- Passwords cracked using GPU rigs: Attackers run hashes through cracking tools at billions per second
- Credential stuffing launched: Bots test email/password combinations against thousands of sites
- Email accounts taken over: Once attackers control your email, they can reset passwords elsewhere
- Financial fraud follows: Bank accounts, credit cards, and payment services get compromised
This entire chain breaks if you use a unique password for every account. The Raaga breach affects one login instead of twenty.
Raaga vs Illinois DHS Breach: Full Comparison
| Feature | Raaga Data Breach | Illinois DHS Data Breach |
|---|---|---|
| Records Exposed | 10.2 million | 700,000+ |
| Data Types | Email, passwords, personal details | Addresses, case numbers, medical info, names (partial) |
| Security Failure | Unsalted MD5 password hashing | Misconfigured system |
| Exposure Duration | Unknown | 3+ years (2021-2025) |
| Primary Risk | Credential stuffing, account takeover | Identity theft, benefit fraud |
| Data Status | For sale on dark web | Under investigation |
What to Do If You Were Affected by These Breaches
You cannot control how companies store your data. You can control how you respond.
Check if your data was exposed:
Visit HaveIBeenPwned.com and enter your email address. The Raaga breach was added on January 19, 2026.
Change compromised passwords immediately:
If you had a Raaga account, change that password. If you used that same password anywhere else, change those too.
Use a password manager:
Stop trying to remember dozens of unique passwords. A password manager like RoboForm or NordPass generates and stores strong, unique credentials for every account. This is the single most effective way to prevent credential stuffing from destroying your digital life.
Test your password strength (free, no tracking):
A password that feels secure might be trivially crackable. Check before you commit to using it.
Enable two-factor authentication:
Even a leaked password cannot hurt you if attackers also need a code from your phone. Turn on 2FA for email, banking, and social media.
Protect your connection with a VPN:
If you are checking accounts or changing passwords on public Wi-Fi, use a VPN to encrypt your traffic. Surfshark and Proton VPN are solid options that will not log your activity.
Monitor for identity theft signs:
For Illinois DHS breach victims: watch for unfamiliar benefit claims, unexpected mail about government programs, or credit inquiries you did not authorize.
Freeze your credit (especially for Illinois victims):
Because the Illinois breach involved government case numbers and demographic data, changing a password is not enough. I strongly recommend a credit freeze. It is free, takes 10 minutes, and is the only way to stop someone from opening a loan in your name using your leaked data.
Freeze your credit at all three bureaus:
The Real Problem: Why Data Breaches Keep Happening
These breaches are not anomalies. They are symptoms of a systemic failure.
Companies treat security as a compliance checkbox. They implement the minimum required to pass an audit and call it done. When security teams recommend improvements that cost money or slow development, leadership says no.
Users pay the price. When Raaga gets breached, Raaga faces bad press and maybe a fine. The 10.2 million users face years of potential fraud.
Government agencies are not immune. Illinois DHS left sensitive records exposed for three years. The systems holding your most sensitive information are not necessarily more secure than a music streaming app.
Regulations lack teeth. A company can use password hashing that professionals abandoned over a decade ago, get breached, and face consequences that amount to a rounding error. Meanwhile, affected users spend hours freezing credit, disputing charges, and proving they did not open fraudulent accounts.
Your data is currency. These organizations leave the vault door open and act surprised when someone walks in.
The only thing that changes this pattern is when negligence costs more than doing it right. Until then, you have to defend yourself.
Protect What You Can Control
You cannot fix corporate security culture. You cannot force government agencies to modernize. You cannot prevent every breach.
But you can make yourself a harder target:
- Use unique passwords for every account
- Use a password manager like RoboForm or NordPass
- Enable two-factor authentication everywhere
- Monitor your accounts for suspicious activity
- Test your password strength before using it
Your passwords are the one piece of this equation you actually control. Make them count.
Frequently Asked Questions
What data was leaked in the Raaga breach?
The Raaga data breach exposed 10.2 million email addresses, names, birthdates, gender, location data, and passwords stored using unsalted MD5 hashing.
What data was exposed in the Illinois DHS breach?
The Illinois DHS breach exposed addresses, case numbers, and medical plan information for 672,000 Medicaid recipients. An additional 32,000 disability services customers had names, addresses, and referral details exposed.
How long was the Illinois DHS data exposed?
The misconfigured system was vulnerable for over three years, from April 2021 through September 2025.
Why is "unsalted MD5" so dangerous?
When you create a password, websites are supposed to scramble it before storing it. MD5 is an old scrambling method that hackers cracked back in 2004. "Unsalted" means Raaga used the same weak scrambler for everyone, so hackers can use a giant cheat sheet to unscramble millions of passwords at once. If your password was anything common, they already have it.
How do I know if my password was leaked?
Check HaveIBeenPwned.com to see if your email appears in known breaches. The Raaga breach is already in their database.
What should I do if I had a Raaga account?
Change your Raaga password immediately. If you used that password anywhere else, change those accounts too. Enable two-factor authentication on all important accounts.
Should Illinois DHS breach victims freeze their credit?
Yes. Because this breach involved government case numbers and demographic data tied to benefits programs, a credit freeze is strongly recommended. It is free and takes about 10 minutes per bureau.
What is the best way to manage unique passwords?
Use a dedicated password manager. Tools like RoboForm and NordPass generate strong passwords, store them securely, and auto-fill them when you need to log in.
Sources
- Have I Been Pwned: Pwned Websites
- HIPAA Journal: Illinois Department of Human Services Data Breach
- TechCrunch: Illinois Health Department Exposed Over 700,000 Residents' Data
- BleepingComputer: Illinois DHS Data Breach Affects 700K People
T.O. Mercer | SafePasswordGenerator.net
Disclosure: Some links in this article are affiliate links. If you purchase through them, I may earn a commission at no extra cost to you. I only recommend tools I have personally vetted.